Understanding the Exploit: What Happened?
A significant vulnerability was discovered in a widely used WooCommerce plugin. This isn’t just a theoretical flaw; it’s an active exploit. Bad actors can bypass security checks, effectively tricking your payment gateway into processing unauthorized transactions.
It means they can initiate charges on your customers’ cards without legitimate consent, directly through your store’s backend processes. This isn’t about phishing; it’s about manipulating your system.
Why This Matters: Beyond Just Money
The direct impact is obvious: fraudulent charges, chargebacks, and potential financial loss. But the damage extends deeper.
Consider customer trust. A single compromised transaction can erode years of brand building. Your customers associate security directly with your brand, not just the plugin.
Then there’s your payment processor relationship. High chargeback rates due to fraud can lead to penalties, reserve requirements, or even account termination. This directly threatens your ability to do business online.
How It Works: A Practical Breakdown
Think of it as an unauthorized back door. The exploit typically leverages a weakness in how the plugin validates user input or processes payment requests.
An attacker doesn’t need to steal card details first. They exploit the plugin directly to tell your payment gateway, “Process this transaction.” Your store, unknowingly, acts as the unwitting facilitator for fraud.
Example: Imagine a smaller online boutique selling handmade jewelry. An attacker uses the plugin exploit to initiate 20-30 small, unauthorized purchases (e.g., $10-$20 each) using various stolen card numbers. These transactions fly under the radar individually but quickly accumulate. The boutique only realizes when a wave of chargebacks hits, weeks later, with their payment processor flagging suspicious activity.
Immediate Action: Secure Your Store
Proactive security is non-negotiable. Don’t wait for your payment processor to flag you.
- Identify & Update: Immediately identify if you are using a vulnerable WooCommerce plugin. Update it to the latest patched version without delay.
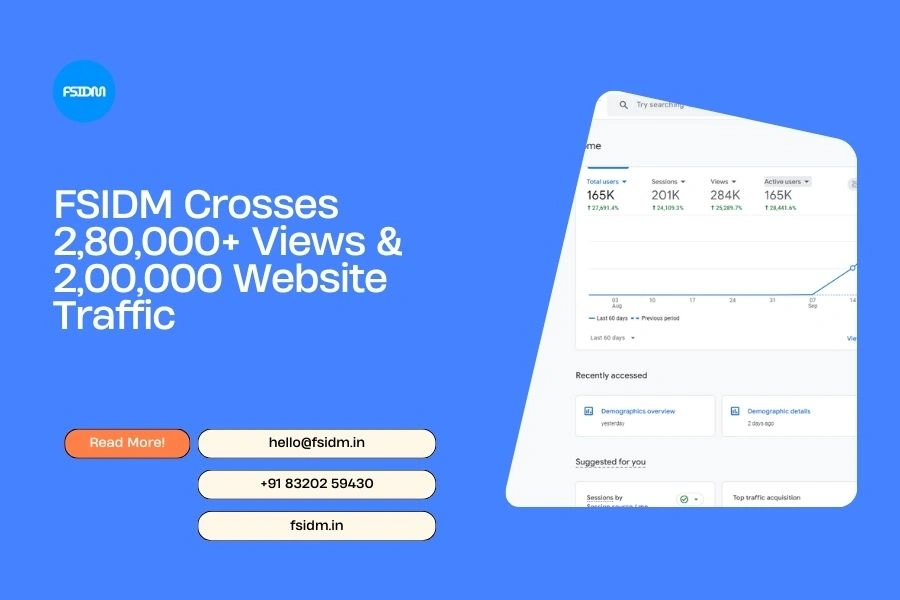
- Audit Transactions: Scrutinize recent transactions for patterns: multiple small orders from unusual IPs, high-value first-time orders, or rapid sequential purchases.
- Monitor Chargebacks: Keep a close eye on chargeback rates. Spikes are a clear indicator of underlying issues.
Frequently Asked Questions
What if I don’t use WooCommerce?
While this specific exploit targets WooCommerce, the principle applies: regularly audit all plugins and extensions for any e-commerce platform you use. Vulnerabilities are constant threats.
Can my customers sue me?
While direct lawsuits are less common for individual fraudulent charges, severe security breaches can lead to class-action lawsuits. The reputational damage and legal fees alone are devastating.
How can I stay ahead of these threats?
Implement a robust security protocol. This includes regular plugin updates, strong passwords, two-factor authentication for admin access, and considering a Web Application Firewall (WAF) for your site.